Tome's Land of IT
IT Notes from the Powertoe – Tome Tanasovski
Category Archives: Registry
Controlling Registry ACL Permissions with Powershell
Posted by on August 28, 2010
Changing Permissions in the Registry
If you want to modify permissions to keys in the registry it’s a fairly simple process with Powershell that is nearly identical to the method you would use for files and folders (thanks to the registry provider). You create an Access Control List (ACL) that lists all of the users who should have access or should be denied access with their appropriate permission type e.g. Domain\powertoe, Full Control, Allow
The easiest method to create the appropriate ACL is to grab the existing one you would like to modify with Get-Acl:
$acl = Get-Acl HKLM:\SOFTWARE\powertoe
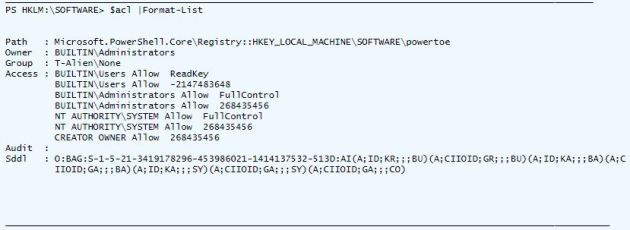
Inspecting $acl will show you the list of access rules that make up the ACL:
To add or remove an access rule you need to create the rule as an object of type RegistryAccessRule, and then either create or remove the rule from the ACL with the SetAccessRule() or RemoveAccessRule() methods:
$rule = New-Object System.Security.AccessControl.RegistryAccessRule ("T-Alien\Tome","FullControl","Allow")
$acl.SetAccessRule($rule)
Now that the ACL is set up to provide the permissions you would like you can pass the ACL into Set-ACL:
$acl |Set-Acl -Path HKLM:\SOFTWARE\powertoe
Putting it altogether you have a very simple way of controlling permissions in the registry via Powershell:
$acl = Get-Acl HKLM:\SOFTWARE\powertoe
$rule = New-Object System.Security.AccessControl.RegistryAccessRule ("T-Alien\Tome","FullControl","Allow")
$acl.SetAccessRule($rule)
$acl |Set-Acl -Path HKLM:\SOFTWARE\powertoe
Changing Permissions when you don’t have access
The above scenario works fine when you have access to change permissions on the registry, but what if you are an administrator and the administrator group has been removed from the ACL. Fortunately, as an administrator I’m still the owner of the key, and I can get these permissions back, but if you try to run the above script you will receive errors like this:
Set-Acl : Requested registry access is not allowed.
In order to do this you will need to connect to the registry via the .NET methods with the specification that you are opening the key for editing with the security access that allows you to change permissions. One of the overloaded versions of the OpenSubkey() method has parameters that let you do this:
$key = [Microsoft.Win32.Registry]::LocalMachine.OpenSubKey("SOFTWARE\powertoe",[Microsoft.Win32.RegistryKeyPermissionCheck]::ReadWriteSubTree,[System.Security.AccessControl.RegistryRights]::ChangePermissions)
The above tells OpenSubKey() to open the key for reading and writing with the desired security access of ChangePermission. Once you have the registry you can set it to any an ACL with the SetAccessControl method. The only caveat is that if you try to use Get-ACL on your key you will receive the access denied messages we saw earlier, but because you already have the key open you can get the ACL using the GetAccessControl() method of the RegistryKey. Putting it all together you get this:
$key = [Microsoft.Win32.Registry]::LocalMachine.OpenSubKey("SOFTWARE\powertoe",[Microsoft.Win32.RegistryKeyPermissionCheck]::ReadWriteSubTree,[System.Security.AccessControl.RegistryRights]::ChangePermissions)
$acl = $key.GetAccessControl()
$rule = New-Object System.Security.AccessControl.RegistryAccessRule ("T-Alien\Tome","FullControl","Allow")
$acl.SetAccessRule($rule)
$key.SetAccessControl($acl)
I’m hoping that the next version of Powershell will make it easier to manipulate ACLs in a much more Powershelly way. I also hope they will give us the ability to natively open the registry keys as we need to. I know this is a more difficult task when you think about how the registry provider is used, but perhaps we need special cmdlets to do these types of functions. In the meantime, the above is a usable workaround that you can look up any time you need to use it.
*Note* I know that I didn’t touch on taking ownership of the registry key if you are not already the owner. It’s a much more unlikely scenario to have in the registry than in your file system, but I’ll get to that in a future article.